Similarly one may ask, what is SIEM and how it works?
SIEM software collects and aggregates log data generated throughout the organization's technology infrastructure, from host systems and applications to network and security devices such as firewalls and antivirus filters. The software then identifies and categorizes incidents and events, as well as analyzes them.
One may also ask, what is SIEM tool used for? Security Information and Event Management (SIEM) is a set of tools and services offering a holistic view of an organization's information security. SIEM tools provide: Real-time visibility across an organization's information security systems. Event log management that consolidates data from numerous sources.
One may also ask, what makes up a SIEM?
A “SIEM” is defined as a group of complex technologies that together provide a bird's-eye view into an infrastructure. It provides centralized security event management. It provides correlation and normalization for context and alerting. It provides reporting on all ingested data.
What are some SIEM tools?
Below we take a look at some of the best SIEM tools on the market.
- SolarWinds Security Event Manager (FREE TRIAL)
- ManageEngine EventLog Analyzer (FREE TRIAL)
- Splunk Enterprise Security.
- OSSEC.
- LogRhythm Security Intelligence Platform.
- AlienVault Unified Security Management.
- RSA NetWitness.
- IBM QRadar.
How is Siem implemented?
7 SIEM Best Practices- Determine Scope. Start by determining the scope of your SIEM implementation.
- Tweak Correlation Rules.
- Identify Compliance Requirements.
- Monitor Access to Critical Resources.
- Defend Your Network Boundaries.
- Conduct Test Runs of Your SIEM.
- Respond Promptly and Comprehensively.
WHY is Siem important?
Companies use SIEM to protect their most sensitive data and to establish proof that they are doing so, which allows them to meet compliance requirements. A single SIEM server receives log data from many sources and can generate one report that addresses all of the relevant logged security events among these sources.What makes a SIEM so powerful on a network?
By correlating process activity and network connections from host machines a SIEM can detect attacks, without ever having to inspect packets or payloads. While IDS/IPS and AV do what they do well, a SIEM provides a safety net that can catch malicious activities that slip through traditional defenses.What does Siem stand for?
Security information and event managementWhat is varonis?
https://varonis.com. Varonis Systems is a software company with headquarters in New York City with R&D offices in Herzliya, Israel. They developed a security software platform that allows organizations track, visualize, analyze and protect unstructured data.How does Siem ArcSight work?
ArcSight ESM leverages the Security Open Data Platform, whose Smart Connectors can connect to 450+ data source types to collect, aggregate, clean, and enrich your data before feeding it into your security analytics. By structuring your data, ESM makes it both more useful and more cost-effective.What is SIEM architecture?
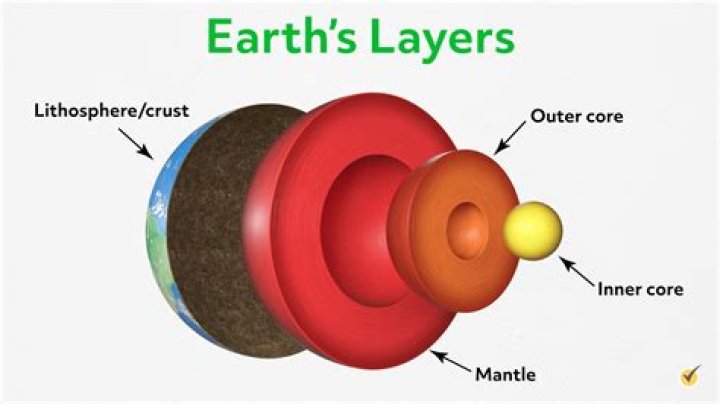
Basically, SIEM architecture collects event data from organized systems such as installed devices, network protocol, storage protocols (Syslog) and streaming protocols.What is a SIEM connector?
You install your SIEM connector behind your firewall. The connector converts the JSON to the data format your SIEM software consumes and sends security events on to your SIEM software. The connector lets you: Define the interval to call SIEM OPEN API and pull in security events.Is splunk a SIEM?
Splunk Enterprise Security (ES) is a SIEM that uses machine-generated data to provide operational insights into security technologies, threats, vulnerabilities and identity information.What is SIEM server?
Security Information and Event Management (SIEM) is a software solution that aggregates and analyzes activity from many different resources across your entire IT infrastructure. SIEM collects security data from network devices, servers, domain controllers, and more.What logs to send to Siem?
The more log sources that send logs to the SIEM, the more can be accomplished with the SIEM.Logs from your security controls:
- IDS.
- Endpoint Security (Antivirus, antimalware)
- Data Loss Prevention.
- VPN Concentrators.
- Web filters.
- Honeypots.
- Firewalls.
What are the problems that Siem solves choose three?
3 Common SIEM Problems Threat Intelligence Can Solve- Information Overload. Problem. The number of interconnected systems and processes in the networks of most organizations today mean that SIEMs often generate somewhere on the order of thousands of alerts daily.
- No Outside View and a Lack of Context. Problem.
- Timing Is Off. Problem.